👉 Practice real hacking labs here
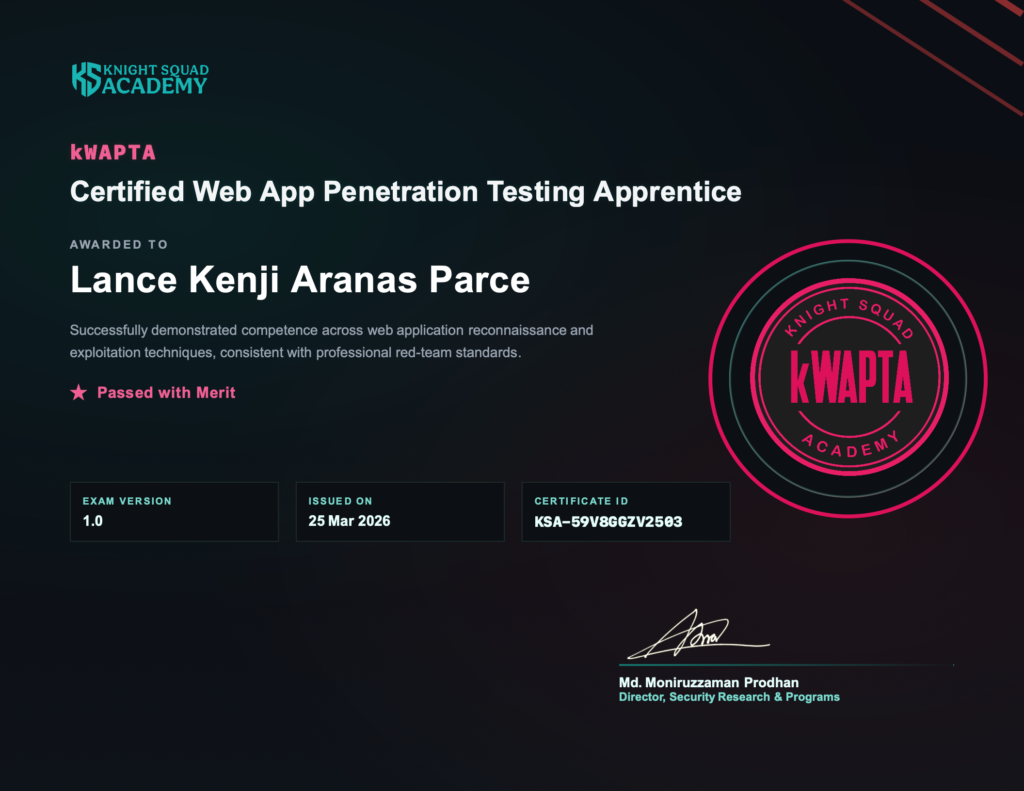
I am thrilled to announce that I have officially earned the Certified Web App Penetration Testing Apprentice (kWAPTA) certification from Knight Squad Academy. Not only did I pass, but I achieved a perfect score of 100%, earning the Passed with Merit distinction
For those unfamiliar with the program, the kWAPTA is a foundation-level certification specifically designed to validate essential, hands-on web application penetration testing skills. Unlike traditional multiple-choice exams, this certification focuses on practical application in a real-world scenario.
A Detailed Breakdown of the Exam
The kWAPTA exam is a rigorous CTF-style (Capture the Flag) assessment conducted in a controlled lab environment. Here are the technical specifics of what the challenge entailed:
Passing Criteria: A minimum of 75% is required to pass, while a score of 85% or above grants the Merit distinction.
Format: 100% practical, requiring the submission of flags as proof of exploitation.
Time Limit: A total of 120 minutes (2 hours). This includes 90 minutes for the actual assessment and 30 minutes for environment preparation, such as instance creation and firewall deployment.
Structure: I had to solve 9 practical questions by penetration testing a dedicated web application.
Difficulty & Pass Rate: While labeled “Foundation,” it is far from easy. The average pass rate is approximately 51%, emphasizing the need for a solid grasp of fundamentals.
The Exam Syllabus
The assessment was comprehensive, covering several critical domains of the OWASP Top 10 and general web security. The scoring was weighted as follows:

- Authorization & Access Control Weaknesses (40%): This was the largest portion of the exam. It involved identifying Insecure Direct Object Reference (IDOR) vulnerabilities, accessing unauthorized data, and finding privilege escalation paths.
- Authentication Weaknesses (20%): Testing login flows and attempting to access restricted accounts without proper credentials.
- Reconnaissance & Application Discovery (15%): Identifying server-side technologies, extracting version information from headers, and discovering sensitive or restricted endpoints.
- Client-Side Injection (12%): Identifying and validating Cross-Site Scripting (XSS) and HTML Injection vulnerabilities.
- File and Path Handling (10%): Assessing the application for improper path handling and file authorization checks.
- HTTP Fundamentals (3%): Understanding request/response headers, cookie configurations, and basic HTTP method handling.
My Personal Experience & Takeaways
What sets the kWAPTA apart is its focus on structured methodology. It isn’t just about finding a bug; it’s about understanding application behavior at the HTTP level and safely validating weaknesses that exist in real-world environments.
The experience was both challenging and rewarding. The access control and IDOR scenarios required a deep understanding of logical flaws rather than just running automated tools. For anyone starting their journey in offensive security, this certification serves as a vital reality check—mastering these basics is essential before moving on to more advanced testing.
Earning this badge is a significant milestone in my career, and I’m looking forward to applying these hands-on skills to build and maintain more secure digital environments.

Are you interested in seeing my official credential? You can verify my certificate using the ID KSA-59V8GGZV2503 on the Knight Squad Academy verification page: https://credential.knightsquad.academy/KSA-59V8GGZV2503
Ready to practice?
Try HackTheBox