Challenge Overview
This challenge focuses on uncovering the origins of the OSINT tool “Holehe”, specifically tracing back the first public appearance and creation date of the creator’s email address.
Behind every OSINT tool is a developer, and behind that developer is usually a publicly exposed email. The task is to identify:
- The creator of Holehe
- The public email address associated with the project
- The exact creation date of that email address
Only the date is required for the final flag.
Flag format:
OSINT{DD-MM-YYYY}
Example (not the real answer):
OSINT{01-01-2020}
Rules:
- Use only legal, open-source information
- Do not contact the developer
- No exploitation or intrusion
- OSINT only (code repositories, public profiles, archives)
Initial Assumptions
Based on the challenge description, the following assumptions were made:
- Holehe is an open-source OSINT tool, likely hosted on a public code repository
- The creator’s email address would most likely be exposed in:
- GitHub repositories
- README files
- Commit metadata
- ProtonMail email addresses may leave public cryptographic or keyserver traces
Investigation Process
1. Identifying the Holehe Repository
The investigation started with a simple Google search:
holehe
This search returned the official Holehe GitHub repository.
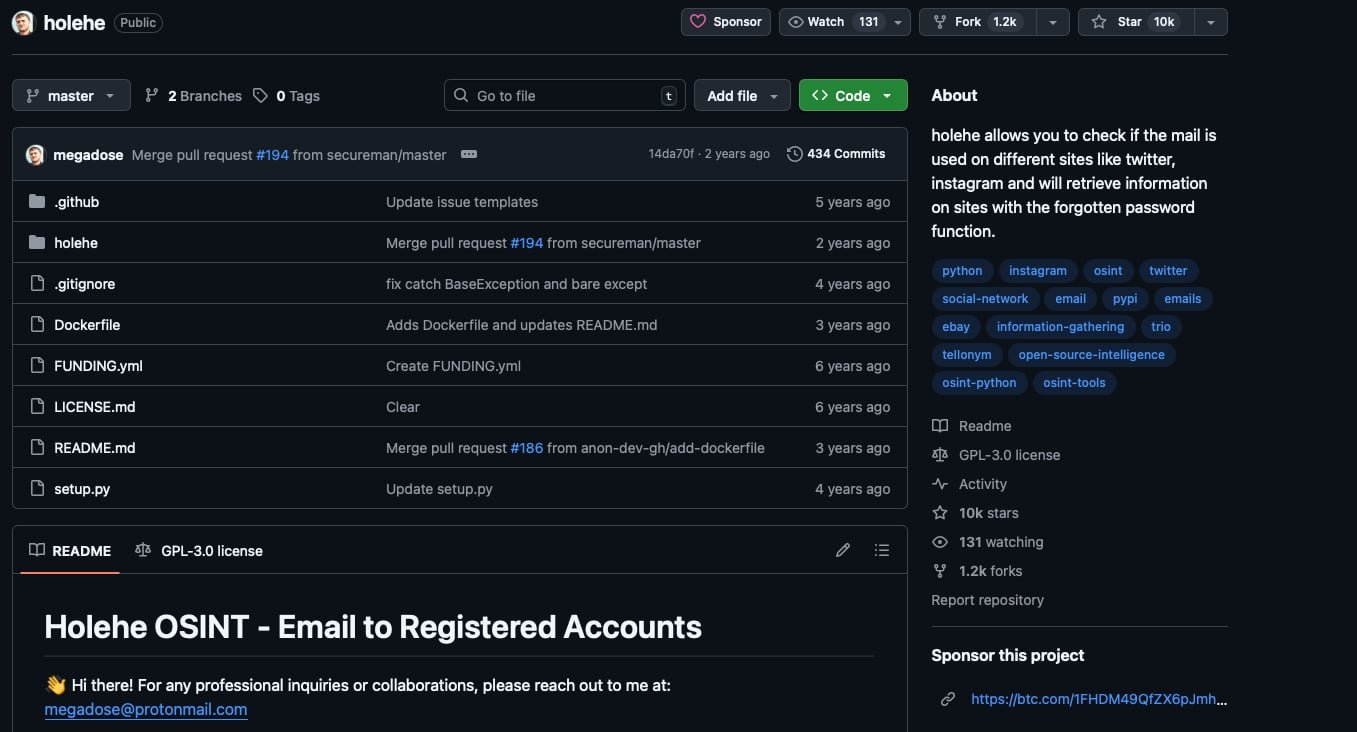
Opening the repository and reviewing the README.md revealed a publicly listed email address used by the creator.
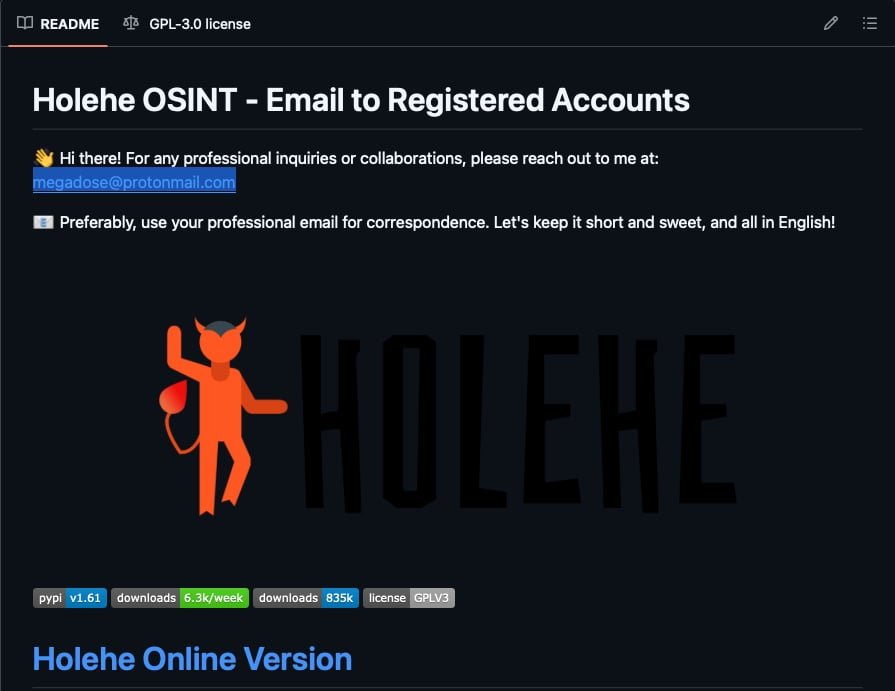
The email found was:
megadose@protonmail.com
2. Understanding ProtonMail OSINT Limitations
ProtonMail does not provide public account creation dates through an official OSINT-friendly API. Searching the Proton website for developer or API documentation revealed a security-related endpoint referenced here:
https://proton.me/security/vulnerability-disclosure
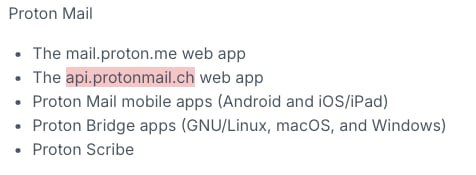
This page references the domain:
api.protonmail.ch
This became the next OSINT pivot point.
3. Google Dorking ProtonMail API Endpoints
Using Google dorking techniques, the following query was used:
inurl:”api.protonmail.ch”
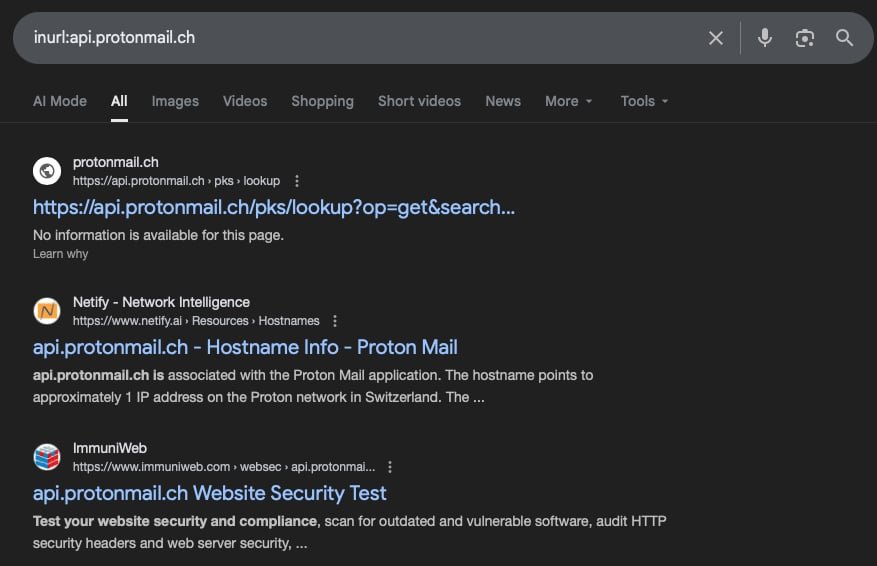
One interesting endpoint discovered was:
https://api.protonmail.ch/pks/lookup?op=get&search=email@protonmail.com
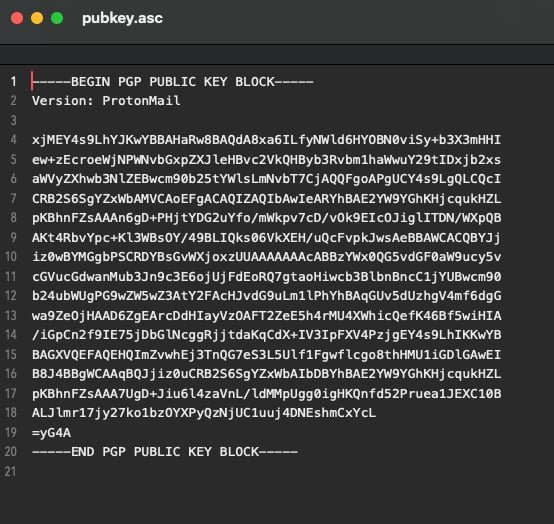
Accessing this endpoint returned an ASC file containing a PGP public key, which suggested that ProtonMail exposes OpenPGP keyserver metadata.
4. Finding an Existing ProtonMail OSINT Tool
To better understand how this endpoint could be used, a search was conducted on GitHub for existing ProtonMail OSINT tools. This led to the discovery of:
https://github.com/C3n7ral051nt4g3ncy/Prot1ntelligence
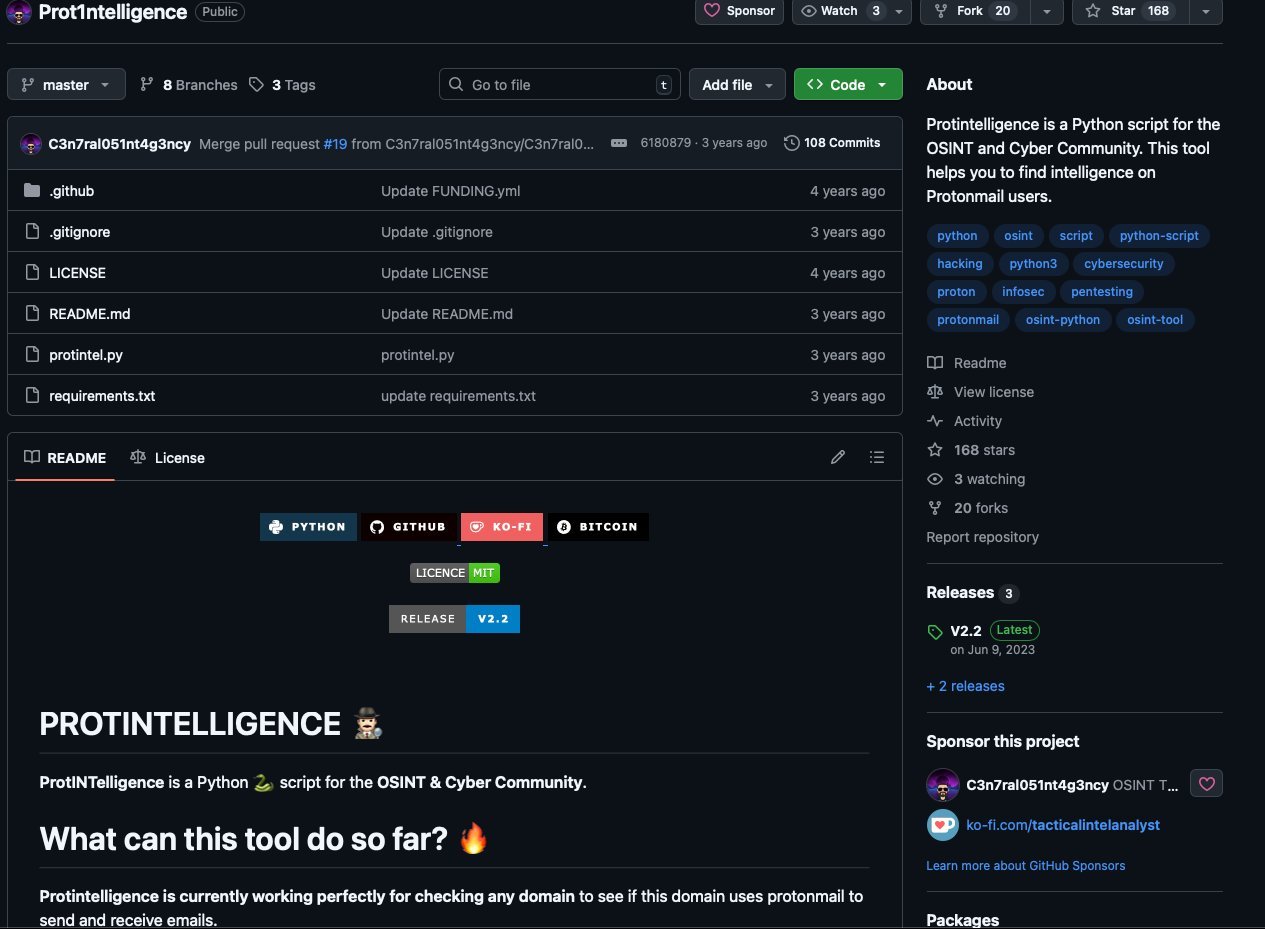
Instead of cloning the repository, the source code was reviewed directly. Inside prointel.py, the following line stood out:

url = f"https://api.protonmail.ch/pks/lookup?op=index&search={email}"This confirmed that the ProtonMail keyserver index could be queried directly using an email address.
5. Querying the Holehe Email Address
Using the discovered endpoint, the following request was made:
https://api.protonmail.ch/pks/lookup?op=index&search=megadose@protonmail.com
The response returned the following data:
info:1:1
pub:b2e401ef07705693a0ccd8d1b0e29d2cac738595:22::1610617266::
uid:megadose@protonmail.com <megadose@protonmail.com>:1610617266::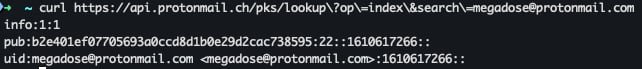
The value 1610617266 appeared consistently and matched the format of a Unix timestamp.
6. Timestamp Conversion
The Unix timestamp 1610617266 was converted into a human-readable date, resulting in:
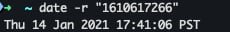
Thu 14 Jan 2021 17:41:06 PST
This timestamp represents the creation or first registration time of the associated ProtonMail PGP identity.
Key Findings
- The creator of Holehe publicly used the email megadose@protonmail.com
- ProtonMail PGP keyserver metadata can expose account-related timestamps
- The Unix timestamp 1610617266 corresponds to January 14, 2021
Final Flag / Answer
OSINT{14-01-2021}
Notes & Takeaways
- Public GitHub repositories often leak valuable OSINT pivots such as emails
- Even privacy-focused services like ProtonMail can expose metadata through PGP key infrastructure
- Understanding how existing OSINT tools work can reveal new investigative paths
- Timestamps hidden in technical outputs are easy to overlook but highly valuable
This challenge highlights how indirect metadata exposure can reveal historical information without any direct interaction or intrusion.