Challenge Overview
This challenge is part of an OSINT training series based on real-world leaked material. Participants are required to remain strictly passive, performing analysis and reasoning only.
The task is to identify the date of birth of an individual whose name appears in a historical dataset linked to an FSB-related leak.
Important constraints:
- No contact with individuals
- No interaction with real accounts
- No harassment or operational use
- OSINT analysis only
Initial Assumptions
Given the nature of the dataset and the information provided, the following assumptions were made:
- The individual is likely referenced in public databases, archives, or watchlists
- Russian full-name formatting (Surname – Name – Patronymic) can be leveraged for precise searching
- The date of birth may already be publicly documented due to leaks or archival publications
Investigation Process
1. Name-Based OSINT Pivot
The only available information was the full name:
КОВЖАРОВА ЕЛЕНА АЛЕКСАНДРОВНАCopy
To minimize noise and false positives, a Google dork using an exact text match was used:
intext:”КОВЖАРОВА ЕЛЕНА АЛЕКСАНДРОВНА”
2. Identifying a Relevant Public Record
The search results returned a relevant entry hosted on Myrotvorets, a publicly accessible archive known for documenting individuals linked to geopolitical and security-related contexts.
Relevant page found:
https://myrotvorets.center/criminal/kovzharova-elena-aleksandrovna-2
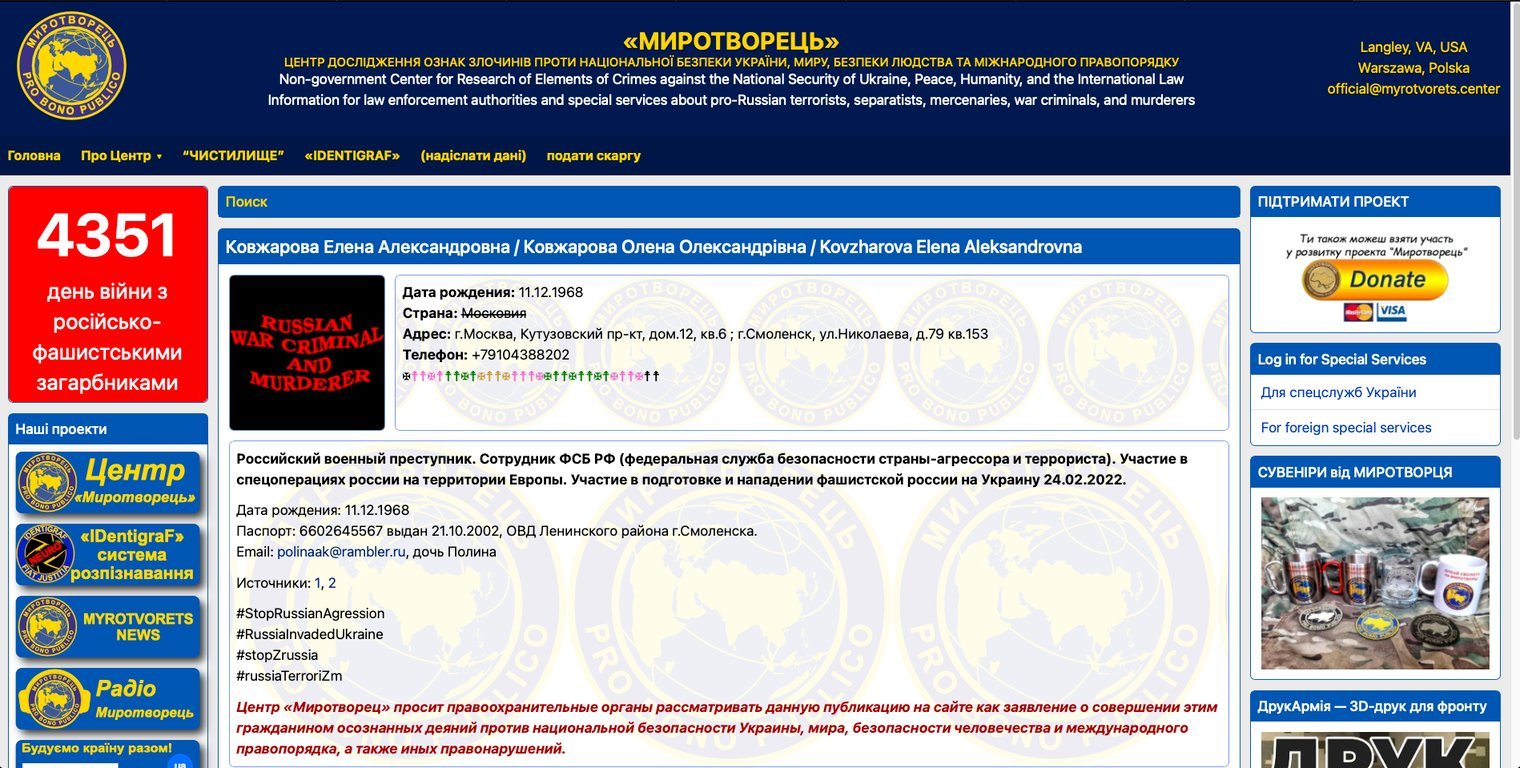
3. Translation and Verification
Since the content was written in Russian, the page was translated into English to verify the details.
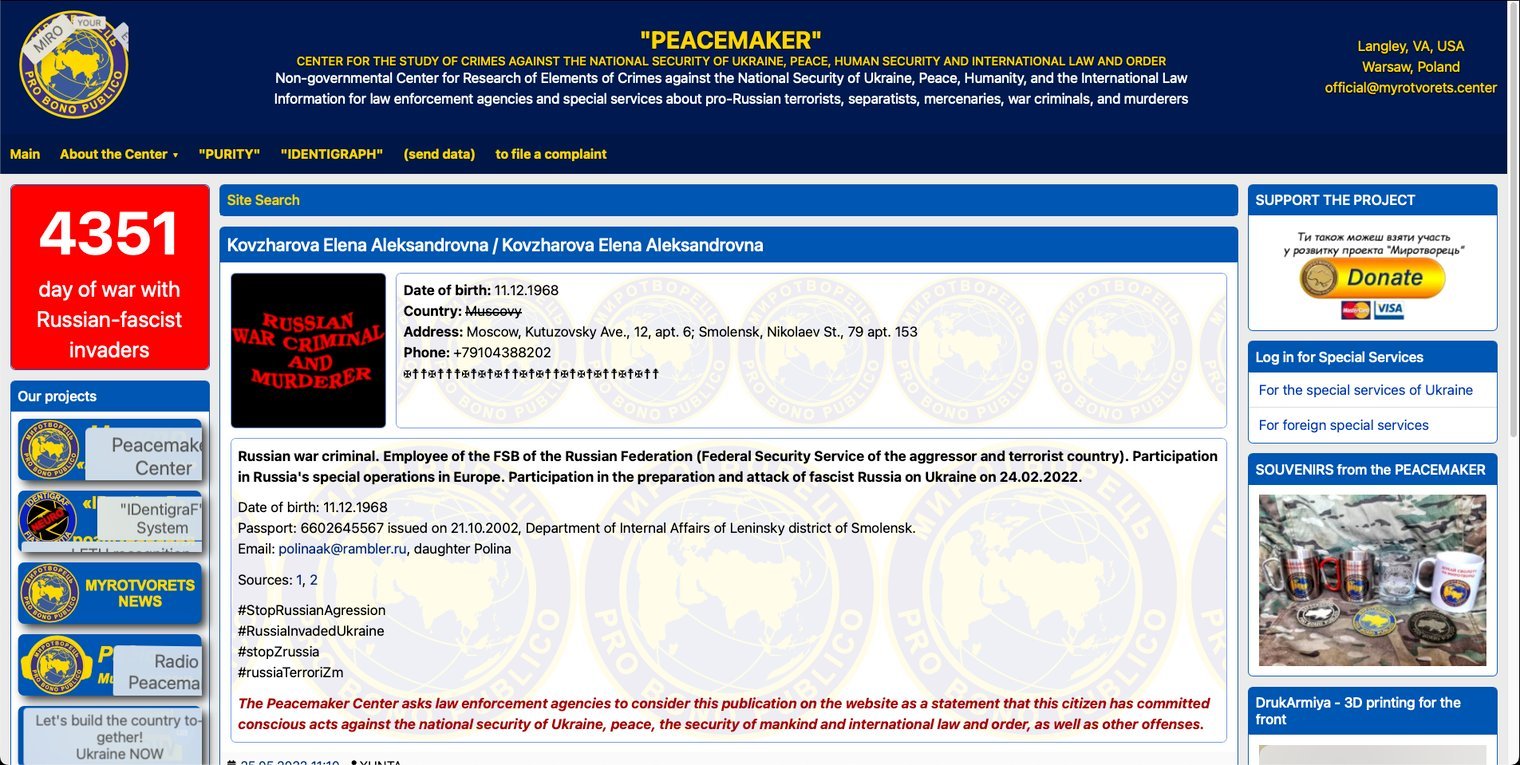
The translated information clearly listed the individual’s date of birth.
Key Findings
- The full name uniquely identified the individual in a public archive
- The Myrotvorets entry contained the missing civil information
- The documented date of birth was:
11.12.1968
Final Flag / Answer
OSINT{11/12/1968}
Notes & Takeaways
- Exact-name Google dorking is highly effective for Cyrillic-based OSINT
- Many historical or leaked datasets are mirrored or archived on public platforms
- Translation tools are essential when working with non-English OSINT sources
- Strict passivity is critical when handling sensitive real-world data
This challenge demonstrates how minimal input data, when combined with precise search techniques, can lead to accurate identification through lawful OSINT methods.